Thunder's blockchain product "chain" is referred to as "disguised ICO"
Today, Thunder announced that its blockchain product chain will not support the transfer function between users, except for the application scenarios developed by Thunder and Thunder partners.
At the same time, Thunder will officially release a new version of the Link Pocket on the AppStore and official website on January 25th. This version will not support the transfer between users except for the application scenarios developed by Thunder and Thunder partners. On January 31, Thunder will complete the full upgrade of the new version of the chain pocket in the mainland.
Yesterday, Speedway.com reported that the China Internet Finance Association issued a “disguised ICO†risk warning. Among them, the focus on the Thunder and its blockchain products “chain gramsâ€, and was referred to as “disguised ICOâ€.
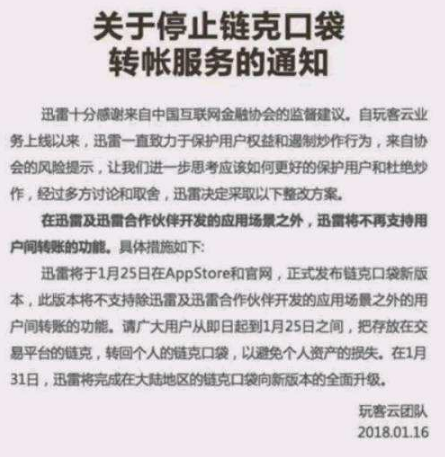
The following is the full text of the Thunder announcement:
Notice on stopping the chain credit transfer service
Thunder is very grateful for the supervision suggestions from the China Internet Finance Association. Since the launch of the customer cloud business, Xunlei has been committed to protecting user rights and curbing speculation. From the risk warnings of the association, let us further think about how to better protect users and eliminate hype. After many discussions and trade-offs, Thunder decided to take The following rectification plan.
In addition to the application scenarios developed by Thunder and Thunder partners, Thunder will no longer support the transfer between users. The specific measures are as follows:
Thunder will officially release a new version of the Link Pocket on the AppStore and official website on January 25th. This version will not support the transfer between users except for the application scenarios developed by Thunder and Thunder partners. Users are requested to transfer the chain stored on the trading platform from the same day to January 25th to return to the personal chain pocket to avoid the loss of personal assets. On January 31, Thunder will complete the full upgrade of the new version of the chain pocket in the mainland.
Application-Specific Integrated Circuit refers to an integrated circuit specifically designed to perform a specific computing task. It is very common to use ASIC for mining in the field of blockchain. This article will analyze the principle of ASIC mining and why it should be anti-ASIC.
For Bitcoin, mining has gone through four stages: CPU, GPU, FPGA and ASIC. GPU is naturally suitable for parallel simple operations, so the execution of SHA256 is much higher than the CPU. FPGA is a programmable hardware, because it has a certain degree of universality, so the unit price will be relatively expensive. ASIC has a large initial design investment, but the unit price will be cheaper after mass production. Therefore, if you can determine that the market size is relatively large, the use of ASIC technology will be the most cost-effective.
This is the basic principle of ASIC.
In a nutshell, mining is running complicated calculations in the search for a specific number. Whether it`s an ASIC miner or a GPU mining rig, mining hardware must run through many calculations before finding that number. In proof of work systems like Bitcoin, the first one to find that number gets a reward - at the time of writing, 12.5 Bitcoins worth around $96,850. That reward will fall to 6.25 Bitcoins in May 2020.
There are so many people and powerful computing systems trying to mine Bitcoin that miner groups form to find that number and share the profit. Even more, the faster your hardware, the more you earn. That`s why people who can afford it opt for ASIC miners because it gives them the greatest chance of earning cryptocurrency in exchange for their investment.
Each cryptocurrency has its own cryptographic hash algorithm, and ASIC miners are designed to mine using that specific algorithm. Bitcoin ASIC miners are actually designed to calculate the SHA-256 hash algorithm. In the case of Litecoin, it uses Scrypt. That means technically they could mine any other coin that`s based on the same algorithm, though typically, people who buy ASIC hardware designed for Bitcoin mine that specific digital currency.
Antin S19J Pro 96Th,Antin S19J Pro,S19J Pro 96T Antminer,s19j pro antminer,s19 xp antminer
Shenzhen YLHM Technology Co., Ltd. , https://www.sggminer.com